CRM 2011 SharePoint 2013 integration ADFS setup for Single Sign On (SSO)
Hi All,
After several hours trying to make this work with the help from technet articles, forums and the help from my colleagues, I managed to get this working. My configuration:
1. CRM 2011 has been configured as IFD using ADFS (see here)
2. My original site is in Default zone (can be either http/https) with Windows Auth
3. I configured ADFS + map LDAP attributes
4. Web application is extended to other zone (in my case Intranet) to be the ADFS site
The reason we can't have 1 site for both Default and ADFS is because the CRM List component does not like the Sign In page when hitting 'Documents' section inside CRM.
The reason we want Windows Auth as well is to be able to crawl the site as well as for admin purposes.
--------------------------------------------------------------------------------------------------------------------
SETTING UP ADFS:
Go to your ADFS Server, open your ADFS management:
1. Add relying Party Trusts with this configuration
• Enter data about the relying party manually, Next
• Enter display name, Next
• Choose ADFS 2.0 profile , Next
• Next
• Click enable support for the WS-Federation Passive protocol. Type in (your going-to-be adfs site url)/_trust/ ,Next
• Type in urn:site:sharepoint and click Add, Next
• Permit all users to access this relying party, Next
• Next
• Close
2. In Claim Rule window, click Add Rule (Issuance Transform Rules tab). Rule template: Send LDAP Attributes as Claims, Next
• Attribute store: Active Directory
• Mapping LDAP Attribute:
sAMAccount Name -> Windows account name
tokenGroups -> Role
userPrincipalName -> UPN
E-Mail-Addresses -> E-mail address
3. In AD FS2.0 -> Service -> Certificates, export the Token-signing certificate (check if there is parent cert or just a single cert as shown in here )
4. Using SharePoint 2013 Management Shell (if there is parent cert need to add parent as well):
$cert = New-Object System.Security.Cryptography.X509Certificates.X509Certificate2("")
New-SPTrustedRootAuthority -Name "Token Signing Cert" -Certificate $cert
$signInURL = (your adfs site)/adfs/ls
$realm = “urn:site:sharepoint”
$samClaimMap = New-SPClaimTypeMapping -IncomingClaimType "http://schemas.microsoft.com/ws/2008/06/identity/claims/windowsaccountname" -IncomingClaimTypeDisplayName "Login" –SameAsIncoming
$upnClaimMap = New-SPClaimTypeMapping -IncomingClaimType "http://schemas.xmlsoap.org/ws/2005/05/identity/claims/upn" -IncomingClaimTypeDisplayName "UPN" –SameAsIncoming
$roleClaimMap = New-SPClaimTypeMapping -IncomingClaimType "http://schemas.microsoft.com/ws/2008/06/identity/claims/role" -IncomingClaimTypeDisplayName "Role" –SameAsIncoming
$sidClaimMap = New-SPClaimTypeMapping -IncomingClaimType "http://schemas.microsoft.com/ws/2008/06/identity/claims/primarysid" -IncomingClaimTypeDisplayName "SID" –SameAsIncoming
$ap = New-SPTrustedIdentityTokenIssuer -Name "ADFS Provider" -Description "ADFS 2.0 Federated Server" -Realm $realm -ImportTrustCertificate $cert -ClaimsMappings $samClaimMap, $roleClaimMap, $upnClaimMap, $sidClaimMap -SignInUrl $signInURL -IdentifierClaim $ samClaimMap.InputClaimType
After several hours trying to make this work with the help from technet articles, forums and the help from my colleagues, I managed to get this working. My configuration:
1. CRM 2011 has been configured as IFD using ADFS (see here)
2. My original site is in Default zone (can be either http/https) with Windows Auth
3. I configured ADFS + map LDAP attributes
4. Web application is extended to other zone (in my case Intranet) to be the ADFS site
The reason we can't have 1 site for both Default and ADFS is because the CRM List component does not like the Sign In page when hitting 'Documents' section inside CRM.
The reason we want Windows Auth as well is to be able to crawl the site as well as for admin purposes.
--------------------------------------------------------------------------------------------------------------------
SETTING UP ADFS:
Go to your ADFS Server, open your ADFS management:
1. Add relying Party Trusts with this configuration
• Enter data about the relying party manually, Next
• Enter display name, Next
• Choose ADFS 2.0 profile , Next
• Next
• Click enable support for the WS-Federation Passive protocol. Type in (your going-to-be adfs site url)
• Type in urn:site:sharepoint and click Add, Next
• Permit all users to access this relying party, Next
• Next
• Close
2. In Claim Rule window, click Add Rule (Issuance Transform Rules tab). Rule template: Send LDAP Attributes as Claims, Next
• Attribute store: Active Directory
• Mapping LDAP Attribute:
sAMAccount Name -> Windows account name
tokenGroups -> Role
userPrincipalName -> UPN
E-Mail-Addresses -> E-mail address
3. In AD FS2.0 -> Service -> Certificates, export the Token-signing certificate (check if there is parent cert or just a single cert as shown in here )
4. Using SharePoint 2013 Management Shell (if there is parent cert need to add parent as well):
$cert = New-Object System.Security.Cryptography.X509Certificates.X509Certificate2("
New-SPTrustedRootAuthority -Name "Token Signing Cert" -Certificate $cert
$signInURL = (your adfs site)
$realm = “urn:site:sharepoint”
$samClaimMap = New-SPClaimTypeMapping -IncomingClaimType "http://schemas.microsoft.com/ws/2008/06/identity/claims/windowsaccountname" -IncomingClaimTypeDisplayName "Login" –SameAsIncoming
$upnClaimMap = New-SPClaimTypeMapping -IncomingClaimType "http://schemas.xmlsoap.org/ws/2005/05/identity/claims/upn" -IncomingClaimTypeDisplayName "UPN" –SameAsIncoming
$roleClaimMap = New-SPClaimTypeMapping -IncomingClaimType "http://schemas.microsoft.com/ws/2008/06/identity/claims/role" -IncomingClaimTypeDisplayName "Role" –SameAsIncoming
$sidClaimMap = New-SPClaimTypeMapping -IncomingClaimType "http://schemas.microsoft.com/ws/2008/06/identity/claims/primarysid" -IncomingClaimTypeDisplayName "SID" –SameAsIncoming
$ap = New-SPTrustedIdentityTokenIssuer -Name "ADFS Provider" -Description "ADFS 2.0 Federated Server" -Realm $realm -ImportTrustCertificate $cert -ClaimsMappings $samClaimMap, $roleClaimMap, $upnClaimMap, $sidClaimMap -SignInUrl $signInURL -IdentifierClaim $ samClaimMap.InputClaimType
--------------------------------------------------------------------------------------------------------------------
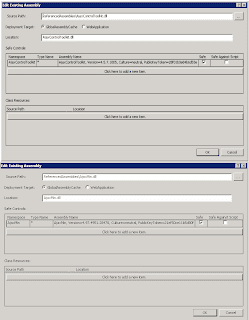
EXTEND WEB APPLICATION
Go to central admin -> Manage Web Applications. Select your default site and Extend web application with following config:
• Port 443
• Hostname
• Enable SSL
• Windows Auth NTLM and Trusted Provider ADFS both enabled
• Zone - Intranet
After creation, configure your SSL certificate, then log in to your ADFS site using your Windows account to add your ADFS users (in this case the Windows account name without the domain since we are using SAMAccountName identifier claim)
Then go back to your Intranet authentication provider to turn off Windows Auth.
From this point, when you go into CRM and access 'Documents' section, ADFS should recognise your token and let you in straightaway.
--------------------------------------------------------------------------------------------------------------------
SEARCH
When you create your search service application, set your content source to be the Default zone site and it should be working nicely.
HTH,
Andreas
Comments
Post a Comment